The healthcare sector has benefited enormously from the widespread use of the Internet and specialized medical computers. Electronic health records, telemedicine, and Internet of Things (IoT) devices are just a few of the benefits that hospitals and practices enjoy in this digital age.
Unfortunately, all this data transmitted back and forth between electronic healthcare devices is a prime target for cybercriminals. As of September 22, 2023, the Office of Civil Rights of the U.S. Department of Health and Human Services was investigating 907 data breaches from the preceding 24 months alone. Each of these breaches involved at least 500 individuals, with the largest affecting over 11 million people. Cybersecurity in healthcare is not just a matter for IT teams; it is a critical concern for every employee at every level of the industry.
Data Sensitivity in Healthcare
Healthcare data is among the most sensitive and private information. It comprises not only patients' medical records but also their personal details, insurance information, and more. Here's why healthcare data is particularly sensitive:
- Personal Health Information (PHI): PHI includes information about an individual's medical history, diagnoses, treatments, and prescriptions. Unauthorized access to this data can lead to identity theft, insurance fraud, or even endanger the patient's life if medical records are altered or misused.
- Financial Information: Healthcare records often contain billing and insurance details, making them attractive to cybercriminals for financial gain.
A data breach in healthcare can result in a loss of trust between patients and healthcare providers. Patients expect their sensitive information to be safeguarded, and breaches can erode confidence in healthcare institutions.
Key Stakeholders in Healthcare Cybersecurity
There are several major stakeholders responsible for cybersecurity in the healthcare landscape. Patients, C-suite executives, workforce members, and equipment vendors/market suppliers are all accountable for enacting or following best practices for cybersecurity.
- Patients must be made aware of how to securely communicate with their healthcare providers. They must also understand privacy and security policies and how to protect their personal information. This is especially important if they interact virtually with their provider, such as over telehealth platforms.
- C-suite executives set the policies that determine a healthcare organization's approach to cybersecurity. Many businesses now employ a chief information security officer (CISO) on par with a chief financial officer or chief marketing officer. The CISO's responsibility is to focus on the business's overall cybersecurity strategy while their subordinates execute it.
- Employees of a healthcare facility are responsible for understanding their organization's privacy and security policies. They must also regularly train in cybersecurity best practices, be able to explain these policies to patients, and know what to do in a cybersecurity emergency.
- Vendors and market suppliers must provide products with rigorous cybersecurity and privacy protection options. Because vendors often have elevated credentials or privileges at multiple healthcare facilities, they must take special care not to suffer a data breach on their end, lest those compromised credentials be used against their customers.
Common Cybersecurity Threats in Healthcare
Cybercriminals have an arsenal of tactics and tools for breaking into a healthcare network and stealing data. These are just some of the ways a hacker can target a healthcare organization's network.
Phishing
Phishing involves fraudulent attempts to deceive individuals into revealing sensitive information, such as login credentials or personal data, by posing as trustworthy entities the recipient is familiar with. Cybercriminals often use fake email or text messages to ask the target to open a link or download a program that requires using their login credentials or other personal information that will later be misused
For example, an employee can receive a seemingly legitimate email asking them to update their login credentials and thus unknowingly provide access to cybercriminals.
Phishing is one of the most common types of cybercrime, as it requires minimal effort on the criminal's part and targets one of the weakest points of any security system: the humans running it. It can lead to unauthorized access to patient records, financial fraud, or the introduction of malware into healthcare systems.
Ransomware
Ransomware is a malicious software that encrypts an organization's data, rendering it inaccessible until a ransom is paid to the attacker. Healthcare institutions are prime targets due to the critical nature of patient data.
If the victim does not pay the ransom, hackers will often upload the stolen data to the Internet or permanently disable the device they've taken control of. Ransomware attacks compromise the privacy and safety of patients and can paralyze the facility's system.
In 2022 alone, the healthcare sector was targeted with 210 reported ransomware attacks. One of the largest, which targeted CommonSpirit Health, affected over 620,000 patients.
Man In The Middle (MITM) Attacks
In an MITM attack, cybercriminals intercept transmitted data as it passes through a network. One of the simplest ways attackers do this is by opening Wi-Fi hotspots in a public place, such as a hospital. These hotspots will often have the place's name in the network but are actually run by malicious actors. Other advanced techniques involve the criminals mimicking IP addresses to reroute people to their fake websites rather than their intended destination.
Whatever their methods, once MITM attackers have access to messages, they can attempt to decrypt and access them. Once this is done, the attacker can use these hacked messages to carry out identity theft, disrupt business operations, and more, depending on the content of the intercepted messages.
Physical Security
Despite the variety of options for remote infiltration, one of the simplest ways for hackers to gain access to a network is by getting their hands on a device used in that network. Once stolen, hackers can use the device to access patient records, insurance information, and more. Even worse, because they are using a registered device on the network, their actions won't be flagged as illegitimate until it is too late to stop them. This is why security features, like SSO and RFID, that only allow authorized personnel to use a healthcare organization's devices are so critical.
Distributed Denial of Service (DDoS) Attacks
A DDoS attack involves a flood of fake connection requests targeting the same server. This causes the server to slow down or crash as it struggles to keep up with the overwhelming number of requests. In the healthcare sector, this can make network resources unusable and leave healthcare providers unable to access patient health records or use their equipment.
DDoS attacks are often used in conjunction with other types of cybercrime. A device already compromised by malware, for instance, can be used as part of a DDoS attack without its owner even realizing it.
Consequences of Healthcare Cybersecurity Data Breaches
Healthcare providers that experience a data breach can face a variety of painful consequences afterward, ranging from financial loss to regulatory repercussions.
Patient Privacy Concerns
Part of what makes healthcare data such a tempting target for criminals is how much private information it contains. For example, medical conditions, treatments, and personal identification details, like contact details, Social Security Number, and financial information are just some of the potential data that can be compromised during a breach.
When these records fall into the wrong hands due to a breach, it can lead to severe privacy concerns, including:
- Identity Theft: Cybercriminals may use stolen patient data to commit identity theft, opening credit lines, obtaining medical services, or engaging in fraudulent activities under the victim's name.
- Stigmatization: Patients may experience social stigma or discrimination if their medical history, such as mental health diagnoses or substance abuse treatments, becomes public knowledge.
- Emotional Distress: Knowing that their private health information has been compromised can cause significant emotional distress for patients, eroding trust in healthcare providers and institutions.
Impact on Patient Care
One of the most immediate consequences of a data breach is losing network access or even a complete device shutdown. This could be something as frustrating as being unable to access a patient's electronic health records or as disastrous as life-sustaining equipment shutting down without warning.
- Downtime: Attacks like ransomware can lead to system downtime, preventing healthcare professionals from accessing patient records and delaying critical medical procedures.
- Data Integrity: Breaches can compromise the integrity of patient records, leading to erroneous treatment decisions and potentially harmful consequences for patients.
- Loss of Trust: Patients may lose trust in healthcare providers and institutions, leading to reluctance to share sensitive information or seek care.
- Resource Diversion: Responding to cybersecurity incidents diverts resources away from patient care, impacting healthcare operations and staff productivity.
Financial Losses
Data recovery costs, legal fees and reputation damage bring the average cost of a data breach in the healthcare industry to roughly $11 million in 2023. That's nearly twice as much as the second-most expensive industry, the financial sector, at $5.9 million per data breach. This cost comes from the interruption of vital services that hospitals cannot afford to let cease, and the prevalence of ransomware attacks against healthcare providers.
Sadly, the number of data breaches and their expenses are increasing yearly as more and more cybercriminals recognize what a tempting target the healthcare industry is.
Legal and Regulatory Consequences
Even after the data breach has been identified and sealed, a healthcare provider's woes may just be starting. Patient health data is heavily regulated, and if a company or provider is found to be negligent in how it stores or protects that data, it can face hefty legal repercussions. HIPAA violations, for example, can cost anywhere between $100 to $50,000 per violation. Particularly negligent offenses can even incur prison sentences.
Class action lawsuits from private individuals are another concern. For example, Johns Hopkins Health System was recently sued after suffering a data breach. The suit accuses Johns Hopkins of being aware of "substandard" IT security, but not acting as well as failing to notify individuals affected by the breach in a timely manner.
Best Practices in Healthcare Cybersecurity
With the threats so prevalent and the consequences so high, healthcare entities must exercise best practices in their cybersecurity more than ever. These solutions and tips will ensure your healthcare organization is better equipped to deal with cybersecurity threats.
Access Control and Authentication
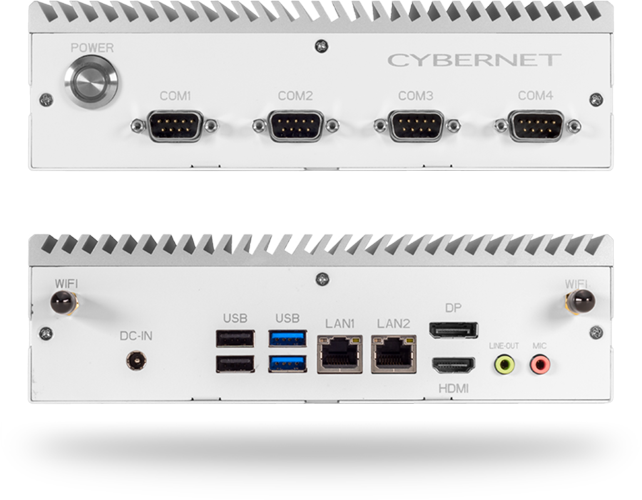
Medical computers often implement access control methods such as RFID readers or smart cards to guarantee physical security. Any individual attempting to use the computer without the proper identification will find themselves locked out. Even something as simple as a privacy screen can prevent prying eyes from spying while a healthcare provider enters their password.
Employee Training and Awareness
The most common type of cyberattack, phishing, relies on the target being unaware and overly trusting. Teaching employees how to recognize and report phishing tactics, and use spam filters correctly can prevent breaches from ever happening.
Similar training for a prompt reaction to a breach notification, using multi-factor authentication, and other cybersecurity basics can go a long way in protecting healthcare organizations.
Encryption and Data Protection
Implementing encryption for sensitive data is a critical layer of cybersecurity. This will ensure that even if malicious actors gain access to your data, they can't do anything with it if they don't have the decryption keys. For this reason, you should only use medical tablets and computers that come with encryption software like Imprivata by default.
Moreover, make sure you regularly back up critical healthcare data and systems to ensure data recovery in case of an incident.
Internet of Things
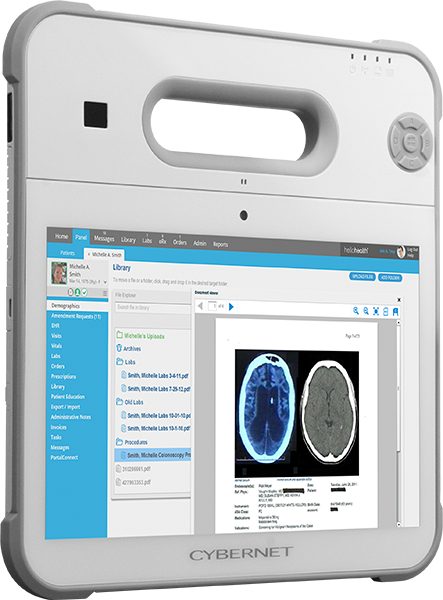
Modern hospitals increasingly rely on wireless device networks interacting with each other as part of an "Internet of Things." For instance, a patient's heart rate monitor can transmit information wirelessly to a healthcare provider's computer for remote monitoring.
However, the issue with these devices is that they often lack strong cybersecurity. This is especially true for older legacy systems that many hospitals still rely upon. By connecting these older devices to a more modern medical computer, a hospital can continue using them while also implementing more modern cybersecurity measures.
Incident Response and Recovery
If the worst occurs and your healthcare organization suffers a data breach, knowing how to respond to it is critical. You should consider incident response the same way you do a fire evacuation plan, as something prepared, updated, and trained for. The quicker your organization can secure its systems and patch vulnerabilities, the less damage you will suffer.
- Develop a comprehensive incident response plan that outlines the steps to be taken in case of a cybersecurity breach.
- Regularly test and update the incident response plan to ensure it remains effective.
- Establish clear communication protocols to inform stakeholders, including patients and regulatory authorities, in the event of a data breach.
Prevent Cyber Attacks With the Right Medical Computers
The number of cyberattacks against healthcare entities and their costs has only been increasing, and this trend shows no signs of stopping. With such heavy consequences, healthcare organizations cannot afford to ignore cybersecurity as part of their priorities.
If your organization is looking to upgrade its cybersecurity, consider Cybernet Manufacturing's range of specialized medical computers. In addition to being designed specifically for medical environments, our computers integrate multiple features to better protect themselves from cybercrime threats, such as Imprivata encryption and RFID scanners to lock out unauthorized access. Contact our experts today, and we can help you choose the right medical computer for your organization's needs.
Join the conversation and connect with us on this and other relevant topics. Follow us on Facebook, Twitter, and LinkedIn.