Cybersecurity in healthcare is one of the sector’s most pressing issues, with 93% of organizations reporting a cyberattack in the last 12 months, according to the 2025 Ponemon Healthcare Cybersecurity Report. This makes healthcare one of the most frequently targeted sectors for cybercrime.
Complicating efforts to protect healthcare operations is reliance on legacy devices, which account for a significant share of tools used but are uniquely vulnerable to malicious actors. Following the best practices for legacy device cybersecurity is not an optional choice for healthcare groups, but an absolute necessity.
Why Do We Need Legacy Device Cybersecurity?
Before we can discuss best practices, we need to define what a legacy medical device is and understand why they’re such a problem for cybersecurity efforts. A legacy medical device is any piece of equipment that is still in use but no longer supported by the original manufacturer for I/O ports, software updates, or bug fixes. This means that if a bug or vulnerability is identified in that device’s software, it will never be patched or corrected by the manufacturer. The concept of legacy hardware and software is not exclusive to healthcare; the Windows 10 operating system became legacy software when Microsoft ended support for it in October 2025, for instance.
However, healthcare is in a uniquely difficult position due to its reliance on legacy tools. Most medical devices can be used for 10 to 30 years, but software lifecycles are much shorter. The cost of purchasing new equipment and the hassle of training staff to use it mean that hospitals prefer to get as much use as possible out of their devices, even if that means going beyond the original manufacturer’s plans for said devices. This is how we arrive at the issue of legacy device cybersecurity: how do we secure and protect mission-critical equipment without breaking budgets or disrupting healthcare workflows?
Legacy Device Cybersecurity Best Practices
With hospitals unlikely to stop using their legacy equipment anytime soon, taking steps to protect their equipment and patients is absolutely necessary. The best practices for legacy device cybersecurity include:
Track Your Inventory Closely
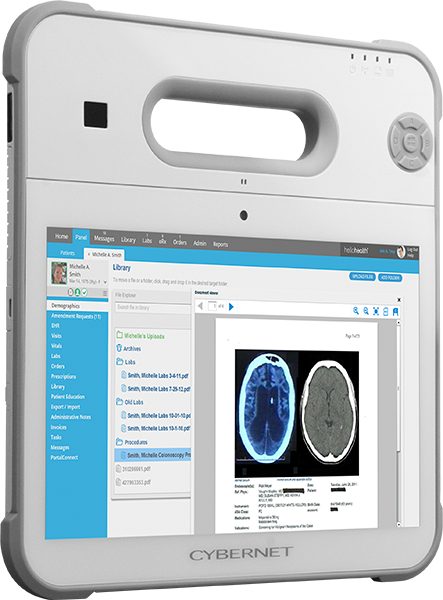
One problem many healthcare groups face is keeping track of which devices are still supported, which have transitioned to legacy status, which require security updates, and which have had massive vulnerabilities identified. Hospital IT teams must stay current with these changes to better identify potential weaknesses in their cybersecurity efforts. Gathering this information also helps decision-makers determine which devices are on the docket for replacement, helping them prioritize the most critical parts of their inventory. Modern medical computers can be used to manage devices, providing a layer of protection between them and the rest of the network or the broader Internet, thanks to built-in encryption and access control methods.
Enforce Network Segmentation
If you cannot protect the device itself, then the best solution is often to protect the network that the device operates on. That’s the theory behind healthcare network segmentation, where operators (such as healthcare groups and hospitals) separate different parts of their networks behind firewalls and virtual local area networks in order to better control the flow of information and access between them. For example, a hospital might have its medical devices work on one network, while its administrative workstations operate on another.
A properly segmented network can limit the spread of malware by making it more difficult to jump from one device to another. The closer monitoring that it provides also means that IT teams can react to breaches sooner, quarantining affected segments before they spread throughout the entire network.
Share Information With Other Groups
A cybersecurity threat to one hospital can be a threat to every hospital still using a particular device. Sharing this kind of information, such as a newly discovered vulnerability, is absolutely critical, but not nearly as well-supported as it should be. Information sharing agreements (ISAs) are sometimes included in other deals, such as non-disclosure agreements and business associate agreements, but they are typically written and developed only within the scope of the deal they’re attached to. A more general ISA template can streamline information sharing between end-users and manufacturers and clarify expectations for security controls, device access credentials, and vendor support.
Develop and Practice a Response Plan
The sad truth is that you will almost certainly be struck by a cyber attack at some point in the future. When this happens, you must have a response plan in place and ready. A hospital should prepare for a data breach the same way it practices fire evacuations or quarantine protocols, with pre-planned responses, subject matter experts assigned to appropriate roles, and the right tools in place before an attack ever occurs. The moment you detect abnormal activity on one of your devices, you should know how to respond to it, just as you would if a fire broke out in a ward. The faster you react, the less damage will be done to your devices and systems.
Benefits of Implementing Legacy Device Cybersecurity
While it is undeniably a challenge, enhancing cybersecurity for legacy devices is not just a benefit for the healthcare sector; it is often an outright necessity.
Greater Security
Obviously, the most significant advantage of taking the effort to protect legacy medical devices is fewer attacks that manage to penetrate your security network, leading to fewer data breaches and less time lost due to disabled equipment. In turn, this means greater safety for both patients and providers, who no longer need to worry about devices failing during treatment or about their identities being revealed and stolen by malicious actors.
Cost Savings
Cybersecurity efforts pay for themselves on two fronts. First, the average data breach in healthcare costs $4.44 million based on global data. This price represents lost work hours due to disabled equipment, the cost of restoring lost data, paying off ransomware, and other expenses incurred when an attack manages to penetrate the network. Thus, enhancing security and preventing data breaches is more than worthwhile on that basis alone.
The second front where legacy device cybersecurity pays for itself is by allowing hospitals to continue using older equipment for longer, sparing them the cost of replacement. For example, if improved network segmentation lets a hospital continue using older ventilators for several more years, that represents thousands, potentially millions of dollars in savings for that hospital. These savings can be reinvested in other critical areas of the hospital’s operations, such as staff compensation, replacing truly obsolete equipment, and maintenance and repairs.
Less Time Spent on Training
Given the pace of modern healthcare operations, providers rarely have the time to train on new equipment or workflows. After all, every hour learning how to use a new ventilator is an hour not spent treating patients who need help immediately. By extending the service lifespan of legacy equipment and reducing turnover, healthcare groups can reduce the time spent on training and familiarization, leading to a more efficient workflow.
Faster Responses to Breaches
The tools and workflows established to ensure greater cybersecurity for legacy devices also enable IT teams to respond more quickly when a breach occurs. With closer equipment monitoring, cybersecurity professionals are more likely to spot unauthorized data transmissions, which is often a sign that the device in question is compromised. Network segmentation means that if a device or group of devices is infected with malware, firewalls can come down and prevent them from spreading the infection.
Keeping Legacy Devices Secure with Cybernet Manufacturing
Protecting legacy medical devices from cyberattacks can be a demanding task, but for many hospitals, it is the only way to keep using the equipment they rely on the most. Protecting these mission-critical devices does require investing time and money, but it is far more affordable than the alternatives.
If your healthcare group is looking for medical computers with modern cybersecurity features to protect its legacy equipment, contact Cybernet Manufacturing. Our range of all-in-ones, tablets, and mini PCs comes equipped with modern cybersecurity features, including Imprivata encryption and access control via RFID scanners and smart card readers.